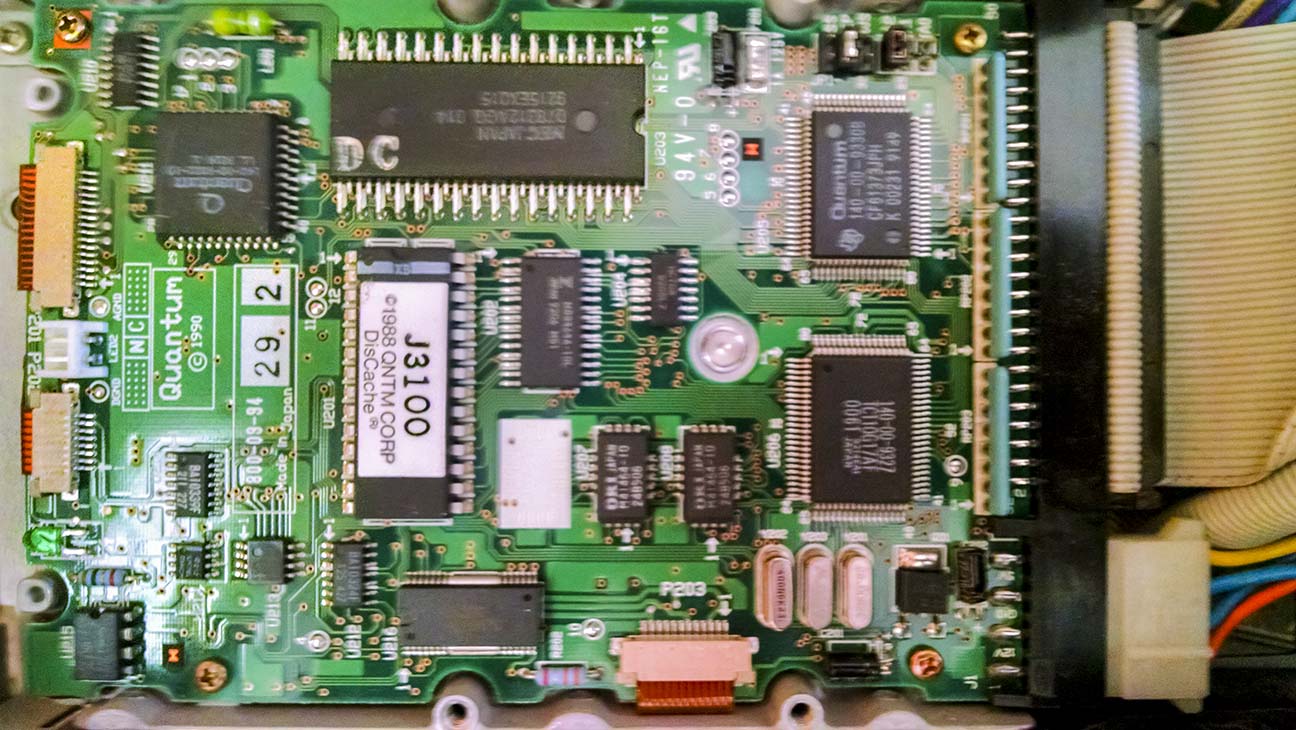
AP Legal, Forensic and Intellectual Property recently faced an interesting challenge — recovering lost Intellectual property (program source code) from a 19 year old SCSI hard drive.
The first steps in the project were to assemble a functional contemporary host computer system capable of both communicating with the SCSI drive, as well as also being capable of transferring the data to a modern storage medium once it had been recovered. In this case, the data stored on the drive was pre-known to be stored in a non-standard specialized filesystem, making it necessary to actually access the drive in-situ from its original host architecture rather than connecting it to a modern computer system with an adapter.
Frequently, working vintage computer systems like this can be obtained from enthusiasts and hobbyists and are often sold on eBay.
The host computer system was upgraded and set up to have the ability to communicate with resources outside of itself by means of a 10 megabit network interface card (NIC). An AUI to 10BaseT adapter was installed to allow the vintage Ethernet adapter to be plugged into a modern network switch, and the TCP/IP protocol stack and network filesystem stack was configured to allow access to storage devices outside the host computer for backup/offload purposes. All of these preparations were made speculatively prior to powering on the target hard drive or knowing if it worked at all. This was done so that if the target drive were functional, everything would be in place to immediately recover data, as many times old equipment may only operate for a very limited time once powered on. Often, a device may power on when first revived, but once it warms up and then cools down after power off, it may never operate again. Frequently, you may have only one chance to recover data, and the clock will be ticking.
Once the working host computer was prepared and operational, the target drive was physically connected. SCSI1 requires a physical termination resistor pack to be installed on the drive at the utmost end of the multi-endpoint SCSI cable. Termination was thus properly configured and the SCSI drive ID set to not conflict with the device IDs of the host computer or the host computer’s boot drive. Optionally, for evidentiary purposes, it is sometimes useful to write-protect the target drive.
At this point, it was possible to start the host computer system and verify that it was able to detect the target drive. Some configuration was necessary at this point to convince the host computer OS to identify and mount the partitions of the target drive using their specialized high-reliability filesystem. Once the filesystem was mounted, a brief inspection was conducted to verify the desired data was in fact present. Deep examination of the data at this point was not done to avoid excess wear and tear and potential premature failure of the target drive.
To complete the recovery, a batch file copy process was initiated to recover the specific desired files. When that successfully completed without errors, a secondary backup of a full block image of the entire drive was conducted, allowing for mounting the device in a virtual machine emulating the original host hardware. The 25-year old Quantum ProDrive performed remarkably well, especially considering it have been stored in a computer case without dust protection, in an outdoor storage facility that was not climate controlled for at least 5 years.
The end result was a successful recovery of important Intellectual Property that had laid untouched for 19 years.